In February of this year a cyber attack on multiple hospitals in multiple places around the globe took place. This was achieved using a software commonly known as ransomware. Ransomware is a type of malware that is installed by hostile agents that prevents or limits users from accessing their own system.
In February of this year a cyber attack on multiple hospitals in multiple places around the globe took place. This was achieved using a software commonly known as ransomware. Ransomware is a type of malware that is installed by hostile agents that prevents or limits users from accessing their own system. After the infection, the agents of the malware notify the attacked parties that they will remove the malware only on payment of a ransom. Hence the term “ransomware”.
This type of malware forces its victims to pay the ransom through certain online payment methods in order to grant access to their systems, or to get their data back (patients data in the case of hospitals). The implications regarding HIPAA compliance are significant.
Although ransomware is usually aimed at individuals, this incident makes it clear that businesses, including those in the healthcare field, can be threatened by these types of cyberattacks as well. The most widely known case of a hospital is in the crosshairs involved in Hollywood Presbyterian Medical Center, in Los Angeles. This resulted in the hospital paying about $17,000 to the attackers to unlock its data. Unfortunately, given the risk, the hospital faced, they had little choice.
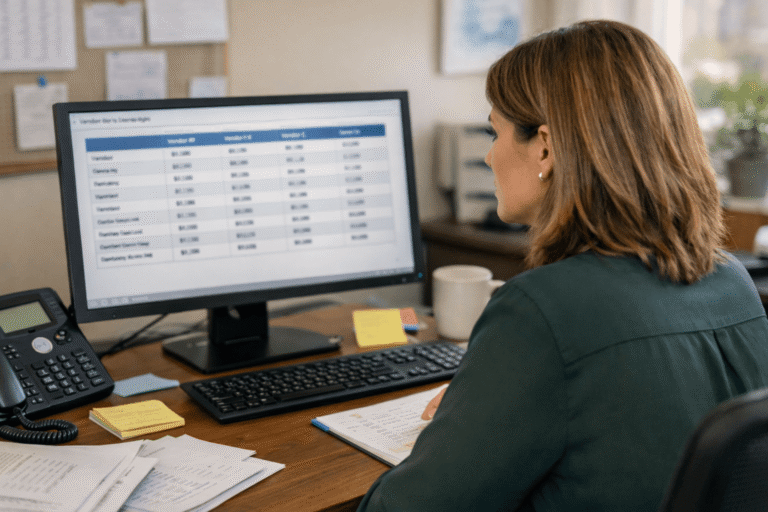
The ransomware attack in California was followed by one in Germany on February 11th, which was generated by an email. This time the hospital involved took a different course of action.
“The hospital said that it had complete backups, meaning that it could wipe and restore affected systems, and noted that all patient data was already encrypted, which forestalled any potential data loss. But as a precautionary measure, the hospital reportedly took all of its systems offline until they were fully restored, rescheduled 20 percent of its surgeries and shifted less-severe emergency care to neighboring hospitals” according to this article.
Of course this method is a fairly extreme measure, and many institutions may not have the same type of backup system that would permit such a restore. The fact that the hospital had all of their files properly encrypted was an obvious advantage.
Titus Regional Medical Center, which is located in Mount Pleasant, Texas was similarly targeted. Their data was forcibly encrypted by ransomware and they were unable to access it. The resulting action taken by the facility is as of yet unknown.
Until recently the targets for ransomware were individuals. And while it may seem obvious in retrospect, the new developments concerning Hospitals caught some off guard. The change in focus to the hospitals is a change in tactic.
The article also explains the similarity of the infection tactic: “the attacks differ little from what’s previously been seen in the wild. Indeed, the mechanics of ransomware attacks are well-known, starting with attackers’ malware-distribution tactics, all the crypto-ransomware we encountered in 2015 was distributed either by drive-by-download attacks or by macro malware in spam emails.”
The recent ransomware encroachments on hospitals is a new development and of obvious concern to anyone working in the healthcare field. What started off as cyber-attacks on individuals has now made the obvious leap to businesses, including reputable hospitals worldwide. As they continue their efforts to target business, steps will be taken to avoid the damage done. But its a learning process, and as it’s a relatively new development sometimes it’s (unfortunately) easier to simply pay the price.
For more information on the recent ransomware incidents involving the hospitals mentioned in this blog please click on the link below.
http://www.healthcareinfosecurity.com/ransomware-hits-hospitals-a-8872